Application performance management (APM) is a crucial practice that entails closely monitoring, measuring, and enhancing the performance and availability of software applications to meet desired...
Search results for: 7 problem management

Entenda a diferença entre incidente e problema em ITSM
O gerenciamento de serviços e o suporte ao cliente são pilares fundamentais para as empresas. O alinhamento dos negócios com a TI, mais do que...

Application performance management in Applications Manager
Application performance management (APM) is a practice that involves the process of managing, monitoring, measuring, and optimizing the performance and availability of software applications to...

Identifique y rectifique proactivamente los problemas de red con la integración OpManager-Jira
Cuando la tecnología evoluciona, se hace increíblemente difícil para los equipos de TI trabajar en el entorno convencional con silos. Las tecnologías como NetDevOps e ingeniería...

Italian luxury car manufacturer escapes fragmented network management with NetFlow Analyzer
Let’s be real, nobody enjoys dealing with a tangled bunch of tools. Especially not when it comes to keeping your company’s network running smoothly. Imagine trying...
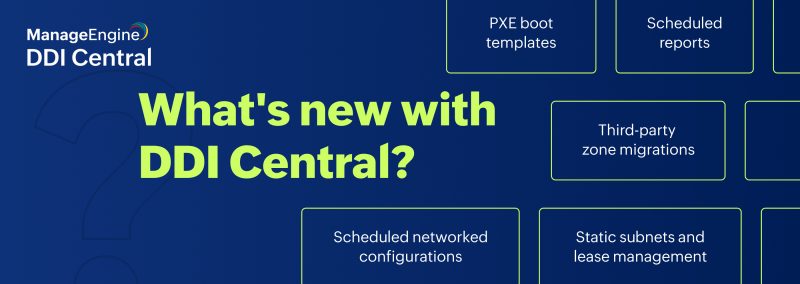
Simplify network management with DDI Central version 4.0.2
The release of DDI Central version 4.0.2 delivers a suite of new features designed to streamline network management and increase the efficiency of various functions...

Diagnóstico de rede: saiba como detectar problemas na infraestrutura de TI
A internet é uma ferramenta necessária em nossas vidas, moldando diversas atividades que realizamos, seja em casa, na rua ou, claro, no ambiente de trabalho....

Identifier et rectifier les problèmes de réseau de manière proactive grâce à l’intégration OpManager-Jira
Avec l’évolution des technologies, il est devenu incroyablement difficile pour les équipes informatiques de travailler dans un environnement conventionnel cloisonné. Des technologies telles que NetDevOps...

OpManager MSP: Your all-in-one solution for multiclient network management
The landscape of network management is undeniably growing in complexity, driven by several factors like: Evolving network complexity: As technology advances, networks become more intricate,...
