Static subnets are the fixed range of IP addresses in the network that are assigned to select individual devices manually. Static subnets differ from dynamic...
Latest Posts

Top tips: 5 potential use cases of 6G networks
Top tips is a weekly column where we highlight what’s trending in the tech world and list ways to explore these trends. This week, we’ll...

The Log360 security platform: Thinking outside the logs
We’re excited to announce the evolution of our SIEM solution, Log360, into a unified security platform. ManageEngine Log360 has adopted an open API-compatible architecture, allowing...
AD360 secures a spot in the Constellation Shortlist™ for Access Management 2025
In the early days, access management meant maintaining static lists of usernames and passwords in directories like Active Directory—a method that served a less interconnected...

Challenges in Kubernetes monitoring and how to overcome them
Kubernetes has revolutionized how organizations deploy, scale, and manage containerized applications, offering unprecedented efficiency and flexibility. However, the very characteristics that make Kubernetes so powerful—its...

Five worthy reads: Algorithmic serendipity—can AI bring back discovery?
Five worthy reads is a regular column on five noteworthy items we’ve discovered while researching trending and timeless topics. This week, we are exploring algorithmic...
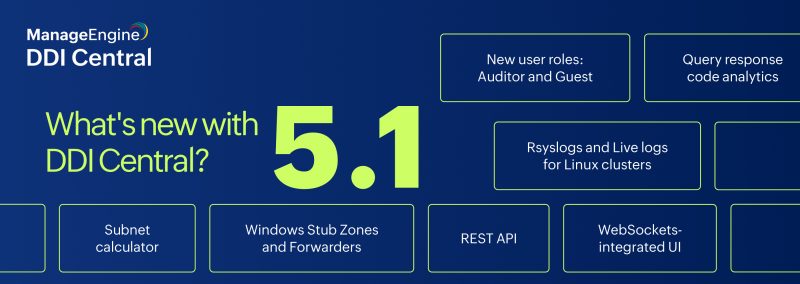
DDI Central 5.1 is here! Supercharge your networks with more power, more control, less hassle
DDI Central has officially launched its latest version, 5.1 (Service Pack 5001), bringing a powerhouse of automation, real-time insights, security, and efficiency to DNS, DHCP,...

Top tips: Integrating biometrics into IAM
Top tips is a weekly column where we highlight what’s trending in the tech world and list ways to explore these trends. This week, we...
IT Security Under Attack: The ultimate playbook to counter cyberthreats
An employee checks their inbox and notices an email from HR with a worrying subject line reading, “Happy New Year! Structural changes in the company...