To stay safe from modern-day pirates, you need elaborate, multi-layered security measures. With the recent exponential increase in data generation and storage requirements, threats to...

Five worthy reads: India’s DPDP Act—a vision for a secure digital environment
Five worthy reads is a regular column on five noteworthy items we have discovered while researching trending and timeless topics. This week we are exploring...

Effortless student account management for a stress-free school year
As the new academic year approaches, IT administrators face a storm of challenges. Did you know that a lot of educational institutions report difficulties in...
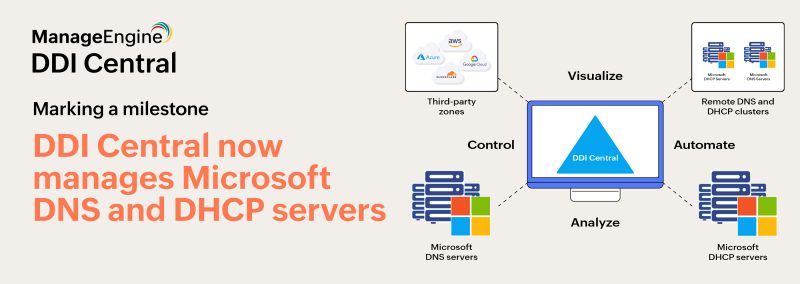
DDI Central is now the ultimate hub for Microsoft DNS, DHCP, and IP address management
DDI Central takes a giant leap forward in simplifying network management for IT infrastructures housing Microsoft DNS and DHCP servers. This is a significant milestone...

Why outdated access control is putting your data at risk
Imagine this: you wake up to a notification – your company has suffered a data breach. Fear sets in as you think about what this...

Top tips: Camfecting—Protect yourself from prying eyes
Top tips is a weekly column where we highlight what’s trending in the tech world today and list ways to explore these trends. This week,...

Has your personal data been breached on the dark web?
The dark web can feel like a mysterious underworld, a hidden corner of the internet where there are no rules. It’s a place where stolen...

How to secure PHI with an identity governance solution
Cyberattacks pose a growing threat across all industries, but healthcare is especially vulnerable. In 2023, hacking incidents in the healthcare sector accounted for 79.7% of...

Combating phishing attacks with passwordless FIDO2 authentication
Attackers predominantly use phishing attacks to steal and misuse user identities. A global Statista study on employee-reported malicious emails revealed that in the first quarter of...
