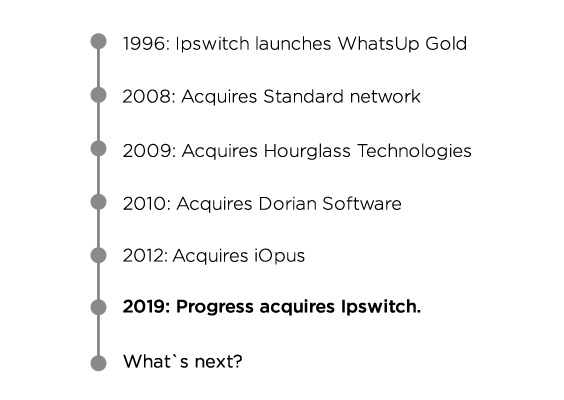
Progress, a provider of application development and digital experience technologies, is set to acquire Ipswitch, a producer of secure data file transfer, mailing tools, and...

Hands-on training awaits at our Dallas User Conference
Our last two User Conferences were abroad, but it’s time to return to the states for our Dallas User Conference. We’re kicking off our first User...

Five worthy reads: How organisations can exploit the potential of enterprise IoT
Five worthy reads is a regular column on five noteworthy items we’ve discovered while researching trending and timeless topics. This week, we address the steady...
How strong are your passwords?
If you’re in IT, you likely know that you should never use weak passwords to secure your business accounts. However, with the average business user...
Still troubled by weak passwords in your Windows environment? Join our webinar to learn about strengthening passwords
As an administrator, keeping your Active Directory (AD) environment secure falls on you! Relying on passwords only for authentication is asking for trouble, especially when users set weak passwords...
Want secure access to Windows logons and multiple cloud apps? ADSelfService Plus is a two for one
Enterprise applications have become an integral part of a tech user’s life. Although the utility and user experience of these applications has been getting better, the risk...
ROI calculators for software: Common problems and our uncommon solution
Often, organizations use ROI calculators to determine the return on investment for using its software. However, the soft benefits—metrics that add value but can’t be measured—cannot be quantified through an ROI calculator, and including them will yield...
Thwart password spray attacks to secure employee access to cloud apps
Chances are you’ve heard of traditional credential-based attacks on Active Directory (AD) and cloud applications—brute force attacks, dictionary attacks, and keylogging, to name a few. There’s now another...

Five worthy reads: Augmented analytics paves the way
Five worthy reads is a regular column on five noteworthy items we’ve discovered while researching trending and timeless topics. This week, we look at the...