ESG research on cyber risk management, which involved 340 cybersecurity professionals, revealed that 40 percent felt tracking patch and vulnerability management over time was their biggest...
Search results for: applications manager

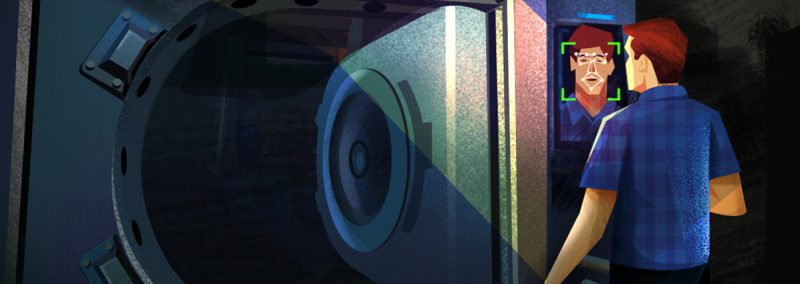
Security operations center, Part 3: Finding your weakest link
Any organization with data assets is a possible target for an attacker. Hackers use various forms of advanced cyberattack techniques to obtain valuable company data;...

ManageEngine makes the cut again for unified endpoint management
There’s no doubt in my mind that Gartner Midmarket Context: Magic Quadrant report is the most important of all Magic Quadrants up to this point....
Five worthy reads: Are we ready for a passwordless future?
Five worthy reads is a regular column on five noteworthy items we’ve discovered while researching trending and timeless topics. This week, we explore the possibilities...
Dangerous defaults that put your IT environment at risk: IT security under attack
In this blog in the “IT security under attack” series, we wanted to shed some light on an unfamiliar and seldom discussed topic in IT security:...
Microsoft Patch Tuesday February 2021 fixes 56 vulnerabilities
With cybersecurity threats on the rise thanks to the pandemic, it is essential to understand the importance of Patch Tuesday releases, and find ways to...
January 2021 Patch Tuesday fixes 83 vulnerabilities
As IT administrators do their best to cope with business continuity plans, it’s imperative that they understand and manage patch updates. With cybersecurity threats on...

Five worthy reads: Decision intelligence for critical business moments
Five worthy reads is a regular column on five noteworthy items we have discovered while researching trending and timeless topics. This week, we explore decision...
IT security under attack: Why are group memberships so crucial?
Security groups either make or break your IT security. Group memberships are responsible for administrative access in your your network and define access to other...
