Pitney Bowes, a global package delivery giant, has been hit by a second ransomware attack in less than seven months, according to ZDNet. Those responsible for the attack have released screenshots portraying directory listings from inside the company’s network.
What is Maze ransomware and what makes it so special?
Maze is typically a sophisticated string of Windows ransomware that has hit several companies across the globe, demanding cryptocurrency payments in exchange for the recovery of encrypted data. Just like any other ransomware, Maze spreads across a corporate network, infects the computers it finds, and encrypts the data.
In what has been observed as a double extortion attack, the attackers steal the data they find, exfiltrate it to malicious servers, then demand a ransom for the safe recovery of data. This makes the Maze ransomware attack a deadly combination of a ransomware attack and a data breach.
Though recovering data from a secure backup might appear to be the solution, the fact that the attackers now have a copy of your organization’s data cannot be overlooked.
What can happen if you ignore their demands?
The attackers now have access to your organization’s sensitive data. If their demands are not met, the attackers can:
-
Release information about the security breach to the public and the media.
-
Impact your stock value by revealing sensitive pricing information.
-
Threaten your clients and partners with their information.
Who are their targets?
So far, Maze ransomware has targeted the IT and health care sectors, professional security services, and law firms. News about the attacks and the proof supporting their claims are released through the attackers’ official website.
How do the hackers enter your network?
The attackers use several techniques to compromise your network. This can include the exploitation of known vulnerabilities that haven’t been patched, the use of remote desktop connections with weak passwords, malicious emails or links, etc.
Best practices to mitigate risks associated with the attack
Some best practices that can help you mitigate the risk associated with the attack are:
-
Backing up data using the 3-2-1 backup rule. This means to have at least 3 copies in 2 different formats, with 1 copy stored off-site.
-
Patch and update applications and programs regularly. This will ensure that the entry points for possible ransomware attacks are blocked.
-
Being vigilant against socially-engineered emails. Often, ransomware attacks are propagated as spam attachments.
-
Ensure that firewalls and intrusion prevention have been enabled in your network.
-
Deploy a comprehensive log management solution that can monitor your network and provide out-of-the-box reports.
How can Log360 help?
Log360, a comprehensive security information and event management (SIEM) solution, helps monitor your network and IT infrastructure and provide real-time alerts and out-of-the-box reports. It provides critical reports based on events, devices, remote connections, and more.
Log360 helps you to:
-
Secure your on-premises, hybrid, and cloud platforms.
-
Thwart security attacks, and protect confidential data from breaches.
-
Gain deeper insights into network activity through in-depth network device auditing.
-
Spot anomalous user and entity behavior.
-
Automate the log management process, including logs from public cloud infrastructure.
-
Audit Active Directory, privileged user activity, and much more in real time.
-
Meet compliance requirements with ease.
-
Quickly implement post-breach actions through extensive forensic analysis capabilities.
and a lot more.
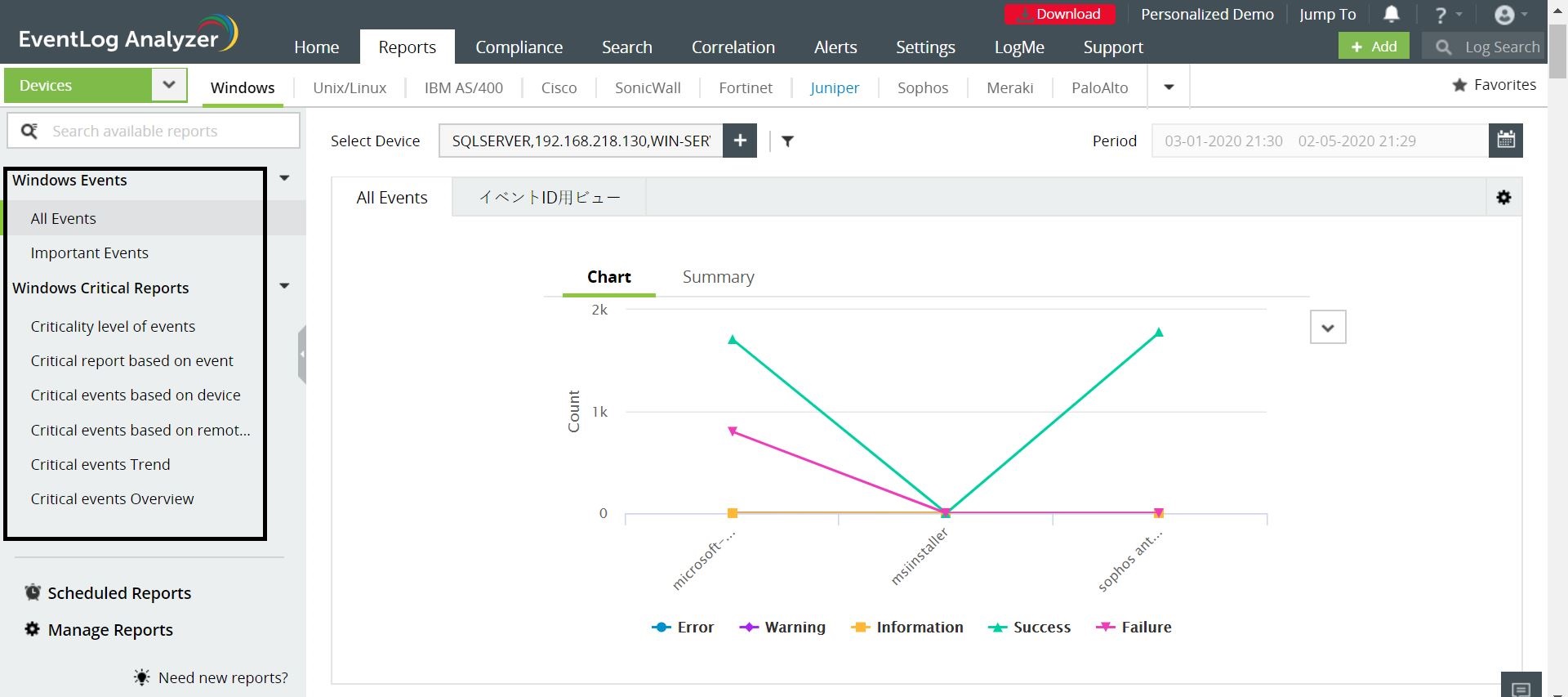
Moreover, Log360 also provides insights on Windows System Events, Threat Detection, Removable Disk Auditing, Network Policy Server, Registry Changes, and more.
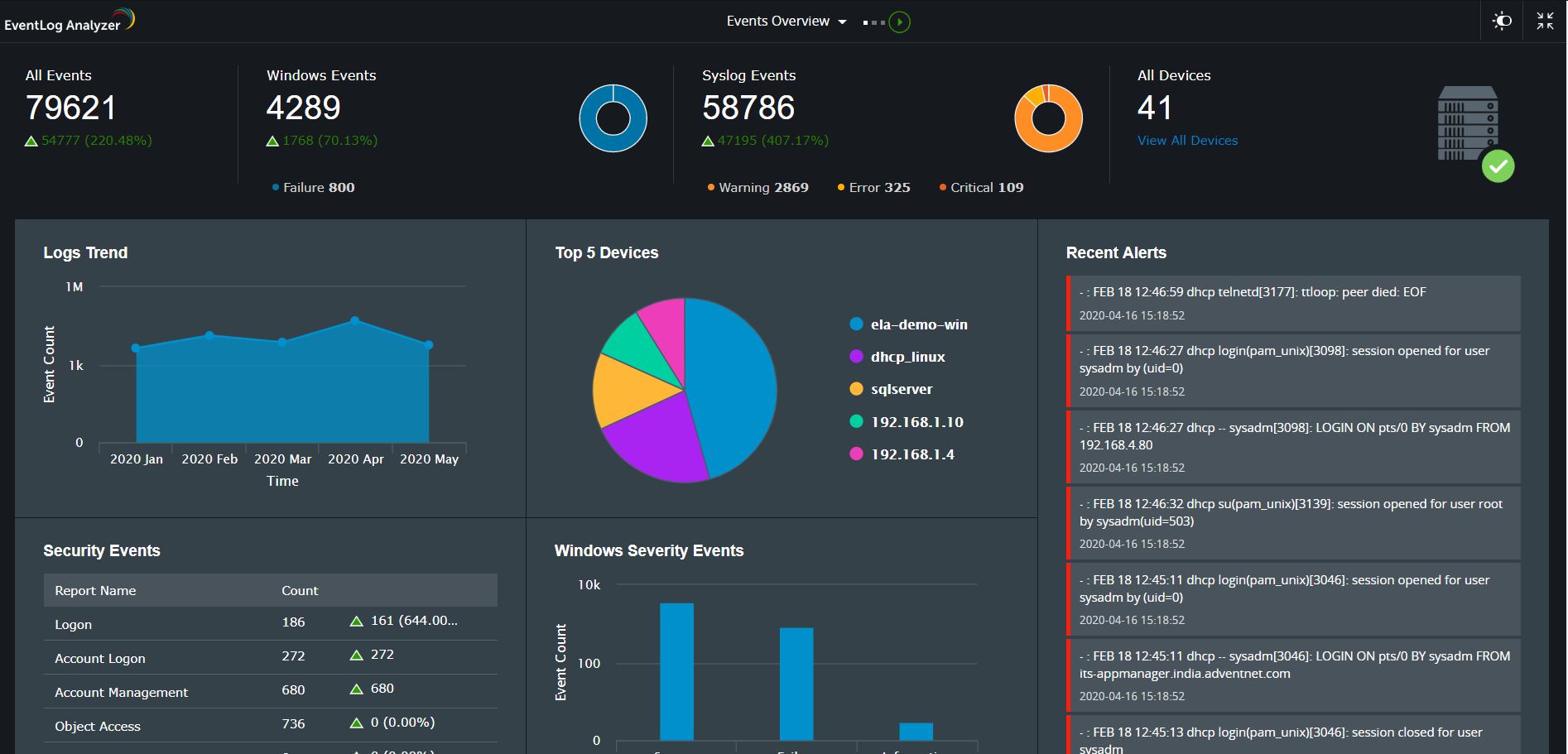
Log360’s log management component, EventLog Analyzer, is integrated with Webroot’s threat feed, which gives a more refined list of threats as it constantly receive updates from endpoint software around the globe. Each malicious IP, URL, or domain updated in the feed is assigned a reputation score that denotes how severe the potential threat caused by it could be.
Log360 leverages the information in threat feeds by correlating it with the log information collected. This ensures you’re alerted when a malicious IP address or URL in the feed initiates a connection with the network.
To try out all these features and more, start your free, 30-day trial of Log360 today.