The “right to be forgotten” is one of the new rights consumers will have under the CCPA. “I’d like to pay with my credit card.”...
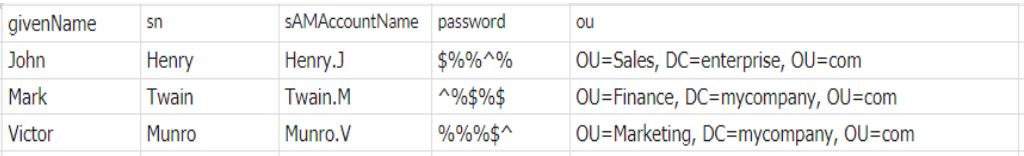
How to create bulk users in Active Directory using a CSV file
Dear admin, Please create Active Directory user accounts, cloud app accounts, home folders, mailboxes, and other requirements for the following new employees. Attached is the list of 100 new members....
2FA based on OU/group membership in hybrid Active Directory
In a previous blog, we saw how two-factor authentication (2FA) secures access to cloud apps in hybrid AD. 2FA adds an extra level of security...

Three critical password management blunders that hackers regularly exploit and best practices to replace them
IT teams often shoulder a number of important security-related responsibilities. It’s essentially up to them to ensure organizations’ networks are secure. For most organizations, comprehensive password...
Five reasons to choose Log360, part 5: Integrated compliance management
So far in this blog series, we’ve seen how Log360 is simple to get up and running, allows you to receive a central view of...
Detecting first time processes on member servers to protect against attacks
In a previous blog, we saw how ADAudit Plus’ user behavior analytics (UBA) capabilities allow administrators to monitor user logon activity to identify compromised accounts....

Complying with NIST password guidelines
Passwords are the most widely used form of authentication across the globe and serve as the first line of defense to critical systems, applications, and data....
Five reasons to choose Log360, part 4: Advanced security features
Part two and part three of this blog series gave a detailed look at Log360’s in-depth auditing capabilities, while part one explained how easy the...

Five reasons to choose Log360, part 3: Comprehensive network auditing
In the previous post, we discussed the various environments that Log360 helps you audit and secure. Having established the ease of Log360’s use and the...

