In preparing for GDPR compliance, you may have heard of Meltdown and Spectre—two new hardware bugs that exist in Intel, AMD, and ARM processors and are capable of exposing any sensitive data processed by countless computers and devices. Personal data like passwords, photos, emails, and even business-critical documents can be accessed and stolen.
These bugs can affect a multitude of different areas in the infrastructure of a computer or device. Both physical problems in the CPU and bugs in the software can create the potential for network breaches. But Meltdown and Spectre differ from these types of bugs as these flaws exist in the architecture of the device’s processor and how it handles sensitive data rather than with the device itself or the software running on it. If a hacker exploits these architectural flaws, they can access the sensitive data processed in physical devices such as desktops, laptops, smartphones, and tablets as well as the sensitive data processed in the cloud.Â
Meltdown’s scope
Primarily, the operating system and user applications work in isolation, and do not exchange data. When raw, unencrypted data is transferred, it is heavily protected against possible prying eyes. Meltdown is a flaw that essentially allows attackers to work around these protections to access the system’s memory and steal sensitive data. Though this flaw exits in the processors architecture, it impacts sensitive data stored on the memory of the devices. Until you update your operating system to mitigate this flaw in hardware, your sensitive data is definitely at risk.
Spectre’s impact
Spectre takes a different approach, tricking applications into disclosing sensitive information that would otherwise be inaccessible. Though Spectre is quite complicated to exploit, it’s equally as difficult to resolve.
Discovery
These flaws were first reported by Jann Horn from Google Project Zero, along with reports from several other enterprises which you can find here. The exploits are CVE-2017-5754 (Meltdown) and CVE-2017-5753 and CVE-2017-5715 (Spectre).
Mitigations
Many vendors have responded to these vulnerabilities with their own updates. Some of these updates are explained in the bullets below.Â
- Microsoft has released a patch for Windows 10, while fixes for other versions will follow soon in this month’s Patch Tuesday updates.
- Apple has already fixed several loopholes in macOS High Sierra 10.13.2, and will further enhance these fixes in the following version.
- Linux has released patches to move the kernel into an entirely separate address space by providing kernel page isolation (KPTI).
- Google has also released updates for Pixel and Nexus devices. Other devices will have to wait for releases of subsequent updates.
- Amazon, ARM, Intel, MITRE, and Red Hat have also released updates to mitigate these threats.
You can find the complete list of security updates from all vendors here.
You can avoid these vulnerabilities by utilizing automatic patch management. ManageEngine offers an escape from these loopholes with support for Windows, Mac, and Linux patches to help you avoid unforeseen surprises and keep your enterprise data safe and secure.
Stay ahead of future Meltdowns or Spectres
If your priority is to secure personal data exploited by vulnerabilities like Meltdown and Spectre, download our automatic patch management solution Patch Manager Plus.
If you want to secure your personal data at all your endpoints, download ManageEngine’s endpoint management solution Desktop Central.
How ManageEngine helps in mitigating these attacks?
The ManageEngine patch management team has already supported patches for the latest Microsoft emergency security update.
If you have configured your patch settings already:Â
- Navigate to the Patch Mgmt tab and click Update Now under Update Vulnerability DB.
- Scan all you your systems, to identify missing patches.
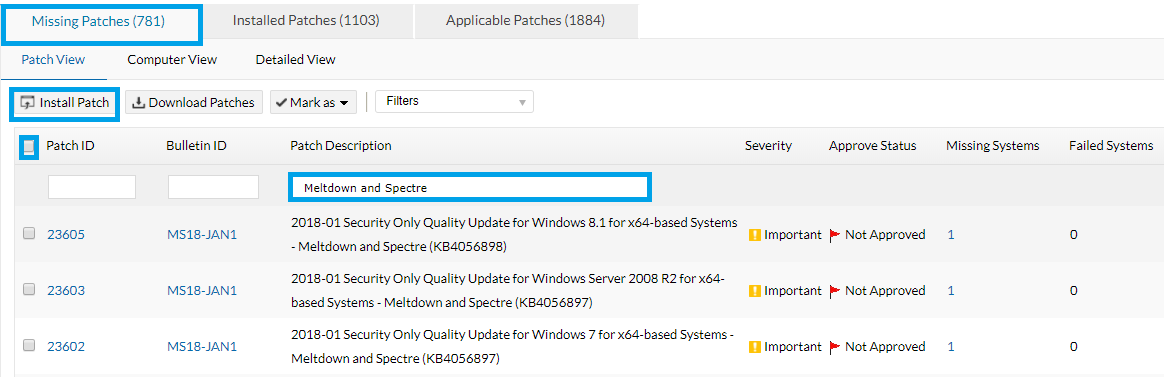
- Search keyword “Meltdown” or “Spectre” under Patch Description Field.
- Select all the missing patches with description about Meltdown or Spectre. Click Install patch to deploy all of them at once.
- You can also verify the installation status of these patches after deployment.
Note: MacOS 10.13.2 have been released to fix these bugs, followed by iOS, Android, Chrome, Linux and other vendors too.
target=”_blank” rel=”noopener”>Meltdown & Spectre webinar for a detailed breakdown.


MEngine cannot provide a list of all machines missing meltdown patches. It can only report machines missing specific patches. Where is the list of all machines missing any meltdown patches? i.e. one list of machines. Good at totals, not good at useful reports.
Hi Bob,
If you have scanned all your systems under each domain, the missing patches with regards to Windows, Linux & Mac will be displayed. Please check this document for more information.
https://www.manageengine.com/products/desktop-central/faqs-on-meltdown-and-spectre.html
When these patches comes directly from Windows Update, it checks if the system has a conflicting antivirus version which is known to cause BSoD (Blue screen of death). If I install these patches using Desktop Central, will it take care of that, or will I end up with a bunch of crashed systems.
If the AV is incompatible, Desktop Central will prompt a warning for you with an Unknown error code, you need to update your AV definitions to the latest before you can deploy MS updates, if in case you do not have a AV in your system, you can deploy this registry key using Desktop Central’s registry configurations. Read more here,
https://www.manageengine.com/products/desktop-central/faqs-on-meltdown-and-spectre.html
Since MS was validating issues with Anti-Virus suppliers of PCs not booting after these updates were applied, they have a registry key that unless present prevents the updates from being deployed.
Is your detection logic matching this and thereby not showing the update available unless the registry key is present?
Yes, we are checking for a specific reg key that will be updated by all AV vendors to provide compatibility for MS updates. Please check this document for a detailed break down.
https://www.manageengine.com/products/desktop-central/faqs-on-meltdown-and-spectre.html