Active Directory (AD) was introduced to the IT world in the mid-1990s, and it has come a long way since then, undergoing several stages of expansion. With the evolution of AD, the attack landscape has also evolved. Attacks have become extremely sophisticated, and attackers are always on the lookout for exploitable opportunities.
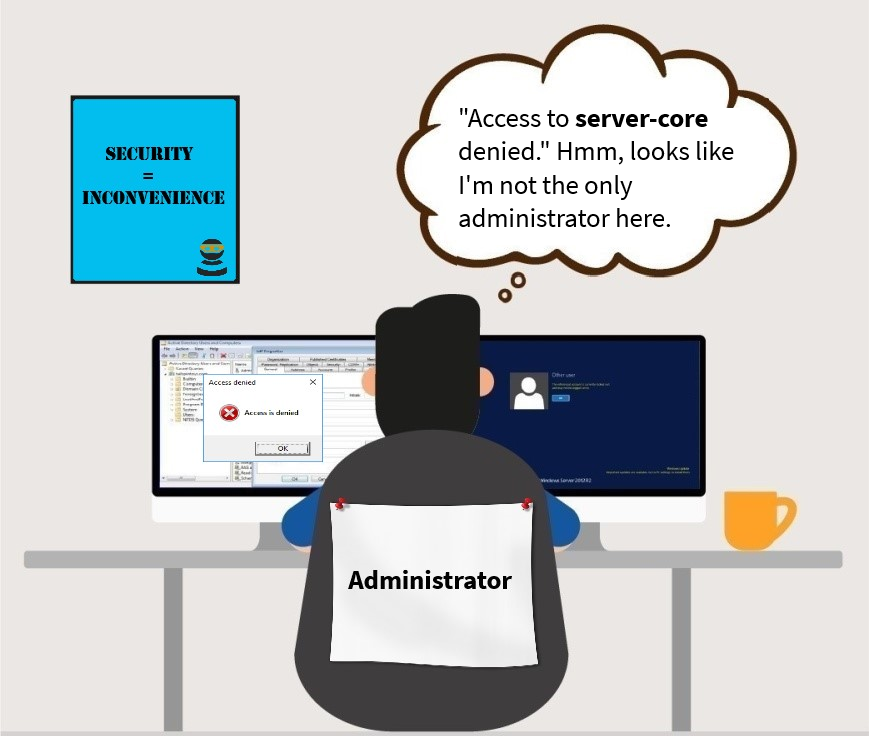
Now, when we hear “attacker” or “hacker,” we often imagine a hooded figure crouched in front of a laptop trying to break the strongest security protocols using their meticulous coding skills. Given AD’s popularity and longevity in the IT world, many think that it takes complex hacking knowledge to break into it. But the truth is that anyone can be an attacker. The utilities and options introduced by Microsoft for the benefit of organizations (around which Microsoft has failed to build sufficient security parameters) are potential access points that can be abused to gain access to privileged accounts in no time. And the worst part? Users need the least privileges to carry out any of these exploits.
Our presentation “There’s more than one way to get admin privileges” provides you with educational content that proves a few key things: Anyone can be an attacker, anyone can be subject to an attack, and you do not need sophisticated tools to perform an attack. All you need is a computer and some motivation!
Instead of the usual information about traditional privilege escalation attacks, this slide deck addresses the various lesser-known techniques that hackers exploit to obtain admin rights, and how attackers can turn the unique selling points (USPs) of Active Directory and Windows ecosystems into exploitable targets just by some careful manipulation. We expose vulnerabilities in AD and Windows that even scripting novices can exploit to gain access to privileged accounts. And most importantly, we also provide countermeasures that you need to take to avoid falling prey to these exploits.
So let’s take this journey to understand AD security from an attacker’s perspective because after all, the best defense only comes when we truly understand the offense.